Founders: Daniel Shechter, Itai Goldman
Year founded: 2023
Field: ADR
HQ: Tel Aviv, Israel
Our multidisciplinary team of experts are always on hand to help you see your vision through. With support tailored to your needs and preferences, we work with you from the earliest stages of your journey to outpace the competition and secure market dominance.
HEAR IT FROM OUR FOUNDERSOur multidisciplinary team of experts are always on hand to help you see your vision through. With support tailored to your needs and preferences, we work with you from the earliest stages of your journey to outpace the competition and secure market dominance.
HEAR IT FROM OUR FOUNDERSWith over 15 years of cybersecurity company-building experience and an in-house team of industry veterans, we offer a broad spectrum of expertise to complement your own. Cybersecurity is our sole focus, and we specialize in helping founders identify and take on the industry’s greatest challenges.
With over 15 years of cybersecurity company-building experience and an in-house team of industry veterans, we offer a broad spectrum of expertise to complement your own. Cybersecurity is our sole focus, and we specialize in helping founders identify and take on the industry’s greatest challenges.
Our global community of cybersecurity experts, potential customers, partners and growth investors hail from the largest companies and firms in the world. Build a full sales pipeline of Fortune 500 companies and tap into a wellspring of advice and knowledge from your target market and seasoned cybersecurity executives.
Our global community of cybersecurity experts, potential customers, partners and growth investors hail from the largest companies and firms in the world. Build a full sales pipeline of Fortune 500 companies and tap into a wellspring of advice and knowledge from your target market and seasoned cybersecurity executives.
Acquired by
Okta
Acquired by
Snyk
Acquired by
Claroty
Acquired by
Elastic
Exited at Unicorn Valuation
Acquired by
Palo Alto Networks
Acquired by
Microsoft
Acquired by
Proofpoint
Acquired by
CA Technologies
Acquired by
Walmart
Acquired by
Radware
Acquired by
Limelight Networks
Exited to
Amadeus Capital
Using in-application context to shed light on your biggest attack surface, Miggo’s ADR enables businesses to monitor how applications behave in runtime and stop attackers from manipulating chains of trust between distributed services. With Miggo, monitor application weak spots, identify and mitigate attacks in real time.
Aim is the industry guide to secure GenAI adoption, equipping security leaders with the ability to drive business productivity while providing the right guardrails and ensuring proactive protection for all GenAI use cases across the entire organization. The company’s GenAI Protection Suite offers security teams unprecedented oversight, visibility, and control to ensure a seamless and secure adoption of GenAI across the enterprise.
The Gutsy platform can track exactly where actions deviate from established best practices and corporate policies and help cybersecurity teams understand which security tools are underperforming. Using Gutsy’s data and reportage tools, cybersecurity leaders can both communicate and optimize their cybersecurity strategies with clarity and ease.
Opus provides security teams with out-of-the-box cloud security and remediation processes, automating and eliminating risk while integrating with existing security tools.
Eureka discovers enterprise cloud data store footprints, data store content, security and compliance risk while continuously monitoring, improving, and measuring cloud data security posture and compliance. With Eureka, enterprise users are free to store, access and leverage data with guardrails that don’t interfere with business agility and operations.
Piiano provides developer infrastructure to protect customer secrets and ensure their privacy–even in the event of a breach. The Piiano Vault enables organizations to safely store sensitive personal data in their own cloud environments with automated compliance controls, saving engineers and security leaders time, effort and resources while achieving secure and compliant applications.
Valence’s SaaS Application Security Platform remediates organizations’ third-party integration, identity, misconfiguration, and data-sharing risks across SaaS applications by automating workflows that engage with business users.
Grip helps security teams discover, prioritize, secure and orchestrate SaaS security for all apps, known and unknown, with full visibility into the organizations’ entire SaaS portfolio,and enforceable endpoint-centric access and data governance capabilities.
Satori’s comprehensive DSP manages access, permissions, security, and compliance policies – all from a single console. Satori continuously discovers sensitive data across data stores and dynamically tracks data usage while applying relevant security policies. Satori enables data teams to scale effective data usage across the organization while meeting all data security and compliance requirements.
Cycode integrates with DevOps tools and infrastructure providers, hardens their security postures by implementing consistent governance, and reduces the risk of breaches with a series of scanning engines that look for issues like hardcoded secrets, infrastructure as code misconfigurations, code leaks and more.
Orcas Security’s Cloud Visibility Platform utilizes its unique SideScanning™ technology to seamlessly deliver comprehensive full-stack visibility into all of your entire cloud infrastructure and assets in a fraction of the time and cost of alternative approaches.
Hunters’ SOC platform empowers security teams to automatically identify and respond to incidents that matter across their entire attack surface. Through built-in detection engineering, data correlation, and automatic investigation, Hunters helps teams mitigate real threats faster and more reliably than SIEMs, ultimately reducing customers’ overall security risk.
Ride Vision is the only Advanced Rider Assistance System (ARAS) on the market specifically designed with the limitations and safety needs of riders in mind. Its industry-leading Collision Aversion Technology (CAT™) is a fusion of Artificial Intelligence and Computer Vision, designed to seamlessly integrate with all motorcycle and scooter makes and models.
With powerful prioritization, orchestration and mitigation capabilities, the Vulcan Cyber risk management platform provides clear solutions to help manage risk effectively. Vulcan enhances teams’ existing cyber environments by connecting with all the tools they already use, supporting every stage of the cyber security lifecycle across cloud, IT and application attack surfaces.
Karamba’s software is designed and implemented to safeguard resource-constrained systems, without interfering with R&D or supply-chain processes.
Acquired by
Okta
Spera offers a proactive approach to identifying and addressing identity-based risks by helping security teams take control of their identity sprawl, manage partially offboarded users, and protect against stolen credentials and account takeovers. The company’s innovative platform provides visibility and contextualized insights into identities, permissions, and actions.
Acquired by
Snyk
Enso empowers organizations to build, manage and scale their AppSec programs. The platform deploys into organizations’ environments to create an actionable, unified inventory of all application assets, their owners, security posture, and associated risk.
Acquired by
Claroty
Medigate provides a dedicated platform for securing networked medical devices that are connected to electronic medical records, device servers, other enterprise systems and the internet. Medigate delivers complete visibility into devices and risk, detects anomalies and actively blocks malicious activities. Medigate enables providers to ensure the delivery of critical treatment and the protection of patient personal and private information.
Acquired by
Elastic
build.security is the first true platform for authorization, providing developers with a simple solution for managing and eliminating the kind of product vulnerabilities that can capsize entire organizations when exploited.
Exited at Unicorn Valuation
Axonius delivers a unified, extensible, and open platform that integrates information from networked devices and existing device-specific standalone management solutions, creating a single visibility and control environment. Axonius dramatically improves an organization’s security and operational posture, allowing IT and security operations teams to safely enable device adoption and usage at scale.
Acquired by
Palo Alto Networks
Twistlock provides the industry’s first enterprise suite for container security. Twistlock’s product addresses risks on the host and within the containerized application, enabling enterprises to enforce consistent security policies from development to production. Twistlock’s innovative technologies monitor container activities, manage vulnerabilities, detect and isolate threats targeting production containers.
Acquired by
Microsoft
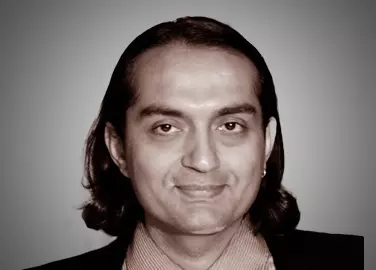
Founders: Eran Barak, Barak Klinghofer, Idan Levin
Field: Cybersecurity Orchestration and Automation
Year Acquired: 2017
Acquired by: Microsoft (MSFT)
Acquired by
Microsoft
Hexadite AIRS is the first agentless intelligent security orchestration and automation platform for Global 2000 companies. By easily integrating with customers’ existing security technologies and harnessing artificial intelligence that automatically investigates every cyber alert and drives remediation actions, Hexadite enables security teams to go from alert to remediation in minutes at scale.
Acquired by
Proofpoint
Founders: Doron Elgressy, Yair Grindlinger
Field: Cloud Access Security Broker
Year Acquired: 2016
Acquired by: Proofpoint (PFPT)
Acquired by
Proofpoint
FireLayers enables the responsible adoption of cloud apps, while ensuring security, compliance and governance of any cloud application on any device by any user. The FireLayers Secure Cloud Application Platform delivers full control over homegrown and popular apps like Salesforce, Office 365, SuccessFactors, NetSuite and endless others.
Acquired by
CA Technologies
BlazeMeter ensures delivery of high-performance software by enabling DevOps teams to quickly and easily run open-source based performance tests against any mobile app, website or API at massive scale to validate performance at every stage of software delivery.
Acquired by
Walmart
Upstream Commerce transforms the way retailers grow sales and boost margins through real-time pricing and product assortment optimization, using state of the art Predictive and Prescriptive Analytics and competitive intelligence tools.
Acquired by
Radware
The Seculert Attack Detection & Analytics Platform, delivered as a service, combines machine-learning based analytics and threat intelligence to automatically detect cyber attacks inside the network, revealing exactly which devices and users are compromised.
Acquired by
Limelight Networks
AcceloWeb is the pioneer and leader in browsing experience optimization, enabling websites to accelerate page load times by factors of 2x to 10x, without requiring server-side code changes or client-side plug-ins. AcceloWeb’s proprietary technology can work with or without content delivery networks to provide near-instantaneous Internet browsing, thereby improving user experience and increasing revenues.
Exited to
Amadeus Capital
Clicktale lights up the digital world, revealing customer behavior, needs and intent. The world’s #1 enterprise-class Experience Analytics platform, Clicktale’s deep-drill downs get to the heart of the “how” and “why” behind customer behavior.






































































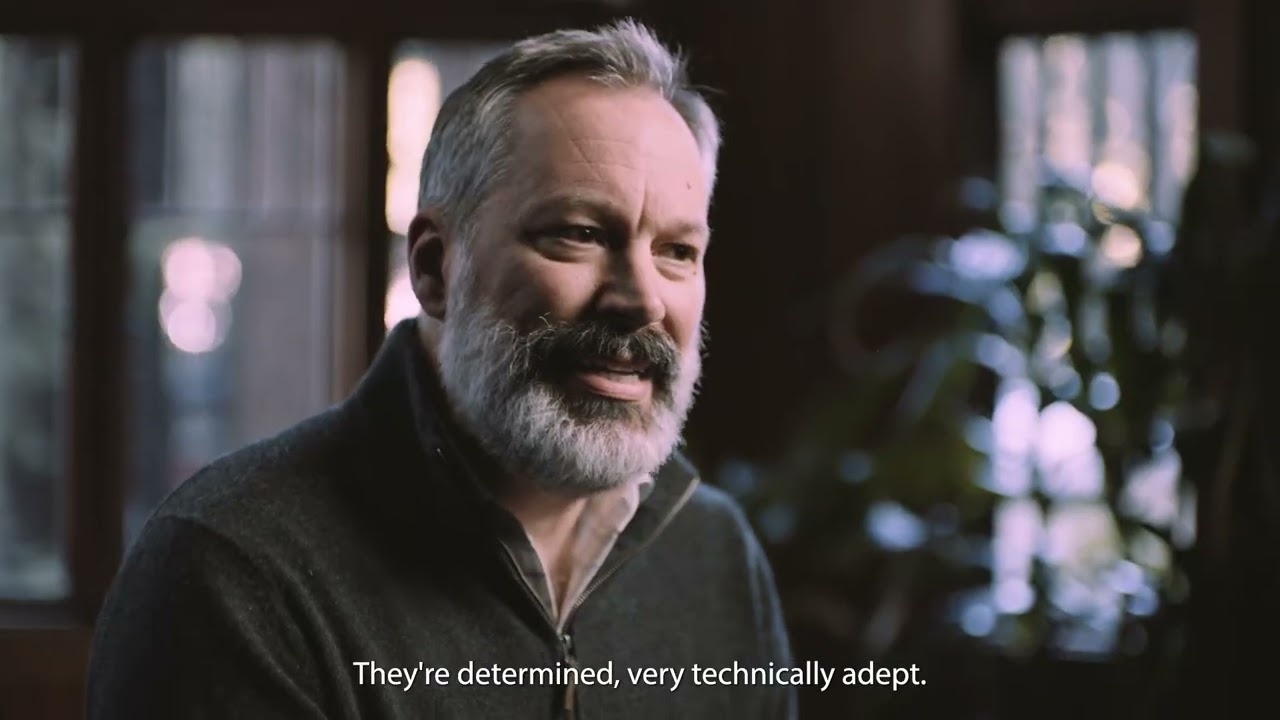
We recently caught up with Justin Somaini, a distinguished #cybersecurity expert and the newest addition to our executive team. After three decades of invaluable experience in various security leadership roles, notably as the CISO of Unity, SAP and Symantec, Justin joined YL Ventures as Partner to lead our US #investment team. During our discussion, Justin…
Check out our recent interview with @JustinSomaini, the newest addition to our executive team. Justin discusses the essential qualities of a successful founder, the market landscape, & why he decided to join @ylventures. Watch the full interview here: https://hubs.la/Q02v14yh0
We recently caught up with Justin Somaini, a distinguished #cybersecurity expert and the newest addition to our executive team. After three decades of invaluable experience in various security leadership roles, notably as the CISO of Unity, SAP and Symantec, Justin joined YL Ventures as Partner to lead our US #investment team. During our discussion, Justin…
Our portfolio company Aim Security is #hiring an experienced Product Designer to join its growing team! This is a one-of-a-kind opportunity to join the founding team, solve complex design challenges from the ground up, and have end-to-end ownership over the product design system. Ping our Talent Acquisition Lead Noy Goldstein for details >> [email protected] #PortfolioJobs…
Our portfolio company @Aim_Security_ is #hiring an experienced Product Designer to join its growing team! Ping our Talent Acquisition Lead Noy Goldstein for details >> [email protected] #PortfolioJobs #startups #cybersecurity
Our portfolio company Aim Security is #hiring an experienced Product Designer to join its growing team! This is a one-of-a-kind opportunity to join the founding team, solve complex design challenges from the ground up, and have end-to-end ownership over the product design system. Ping our Talent Acquisition Lead Noy Goldstein for details >> [email protected] #PortfolioJobs…
“Determined to bring a similar level of visibility and understanding to the application layer, we envisioned a solution that could map, baseline and contextualize the intricate interactions between application components to proactively identify and mitigate threats. The more we’ve worked on this, the more Application Detection and Response (ADR) felt like the only natural next…
Don’t miss the chance to connect with our portfolio company @Eureka_Sec at the @RSAConference and learn more about their comprehensive #DSPM platform! Find a time to chat with their team, here: https://hubs.la/Q02tY36r0
“Determined to bring a similar level of visibility and understanding to the application layer, we envisioned a solution that could map, baseline and contextualize the intricate interactions between application components to proactively identify and mitigate threats. The more we’ve worked on this, the more Application Detection and Response (ADR) felt like the only natural next…
In the spirit of Passover, where Jewish families worldwide sit down to ask the Four Questions, The Jerusalem Post asked Partner, Marketing Sharon Seemann four questions of their own. Against the backdrop of recent challenges, including the aftermath of the October 7 massacre and economic uncertainties, Sharon shared her perspective on the current and future…
We are thrilled to welcome @MiggoSecurity – the first Application Detection & Response solution – to the @ylventures portfolio and look forward to seeing them transform the #AppSec landscape. Learn more about Miggo on CEO Daniel Shechter’s blog: https://hubs.la/Q02tBXyK0
In the spirit of Passover, where Jewish families worldwide sit down to reflect and ask the Four Questions, The Jerusalem Post asked Partner, Marketing Sharon Seemann four questions of their own. Against the backdrop of recent challenges, including the aftermath of the October 7 massacre and economic uncertainties, Sharon shared her perspective on the current…
“Miggo’s the missing piece to full stack visibility. Traditional #AppSec tools are still analyzing code in a vacuum. Of course, static code analysis is critical, but it can never translate into real-time security. Miggo is breaking the mold by extending AppSec’s reach to the application itself. For the first time, a solution is offering real-time,…
In the spirit of Passover, where Jewish families worldwide sit down to reflect and ask the Four Questions, the @Jerusalem_Post asked Partner, Marketing Sharon Seemann four questions of their own. Read Sharon’s full interview, here >> https://hubs.la/Q02ty10R0
“Miggo’s the missing piece to full stack visibility. Traditional #AppSec tools are still analyzing code in a vacuum. Of course, static code analysis is critical, but it can never translate into real-time security. Miggo is breaking the mold by extending AppSec’s reach to the application itself. For the first time, a solution is offering real-time,…